Interpres Security launched out of stealth-mode in December 2022… And since then we’ve been hard at work building and expanding the Interpres Threat Exposure Management Platform and delivering unique features based on customer needs. We’d like to detail some of the new and exciting features coming to the platform. We think that these recent feature releases will enhance our customers’ ability to defend themselves against the threats that matter most by continuously analyzing, prioritizing, and optimizing their security posture.
Notional Data
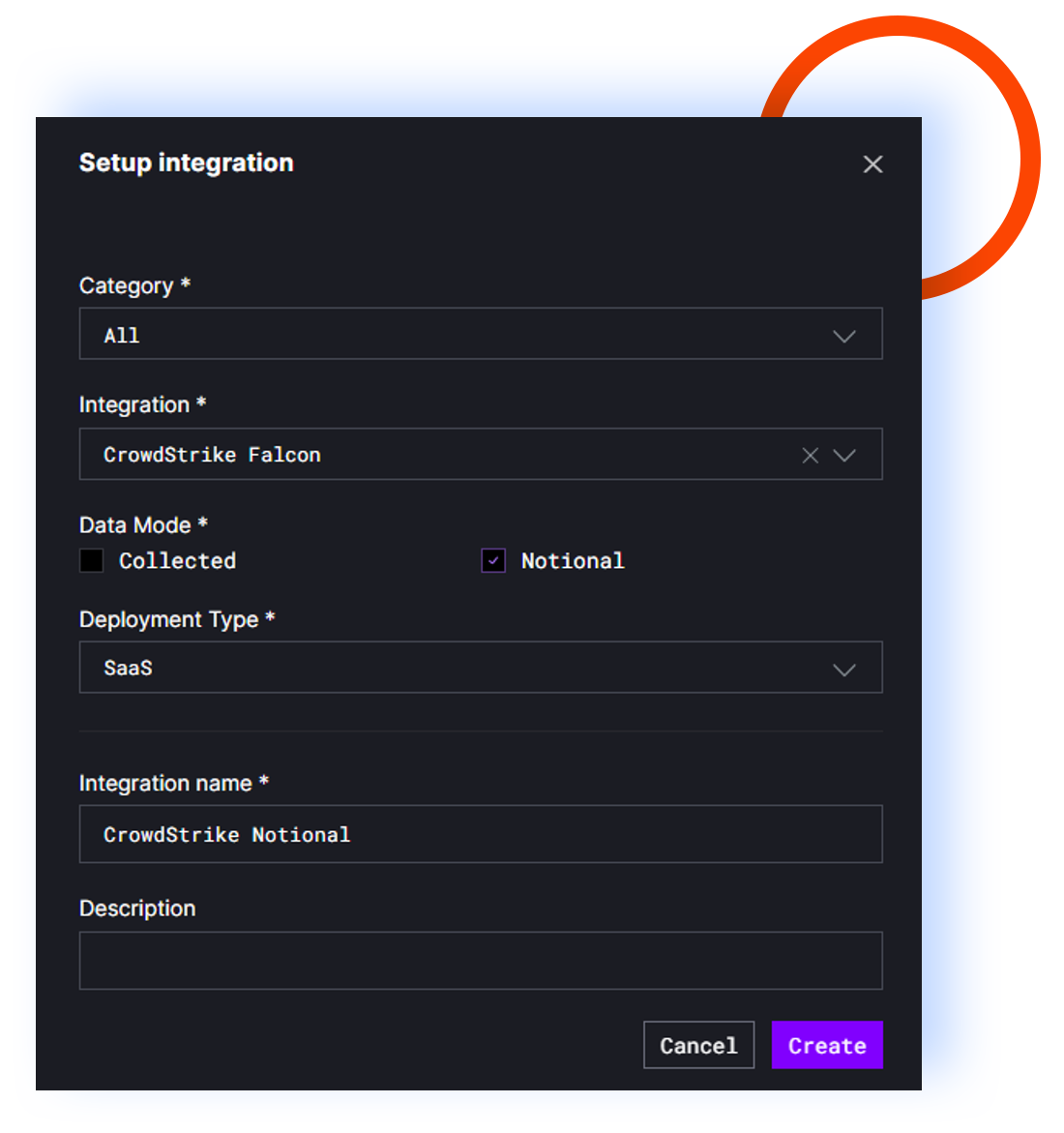
We think it’s vitally important to start with a complete and accurate picture of a customer’s security posture. To accomplish this, we have 35+ integrations with leading security products that connect to your products via API with read only permissions. These integrations continuously poll for changes in your security posture, letting you know when something changes, or if anything is unoptimized to address your unique threat. This is the only practical way to validate your security strategy, optimize your product stack, and improve your defensive capabilities by minimizing your threat exposure.
Notional Data, or data gathered from a third party (such as an Endpoint Detection and Response vendor), is not enough on its own to make decisions about your security posture or threat exposure. This is because no security product is configured the same across organizations. However, we do believe Notional Data can be beneficial as another data point and in cases where it may not be possible to connect to a security product.
Threat Intelligence Integrations
Within the Interpres Threat Exposure Management Platform, we freely provide TTP-based threat intelligence from 22+ various sources. This allows us to provide customers with the most recent campaign data across the threat landscape. However, we’ve heard from customers that they would like to leverage threat intelligence from the premium feeds that they already have access to or pay for.
We now support threat intelligence integrations that allow customers to connect to their threat intelligence products and use that data within Interpres. We are shipping an OpenCTI integration and are currently working on others. Understanding your readiness as it relates to adversarial campaigns has never been easier.
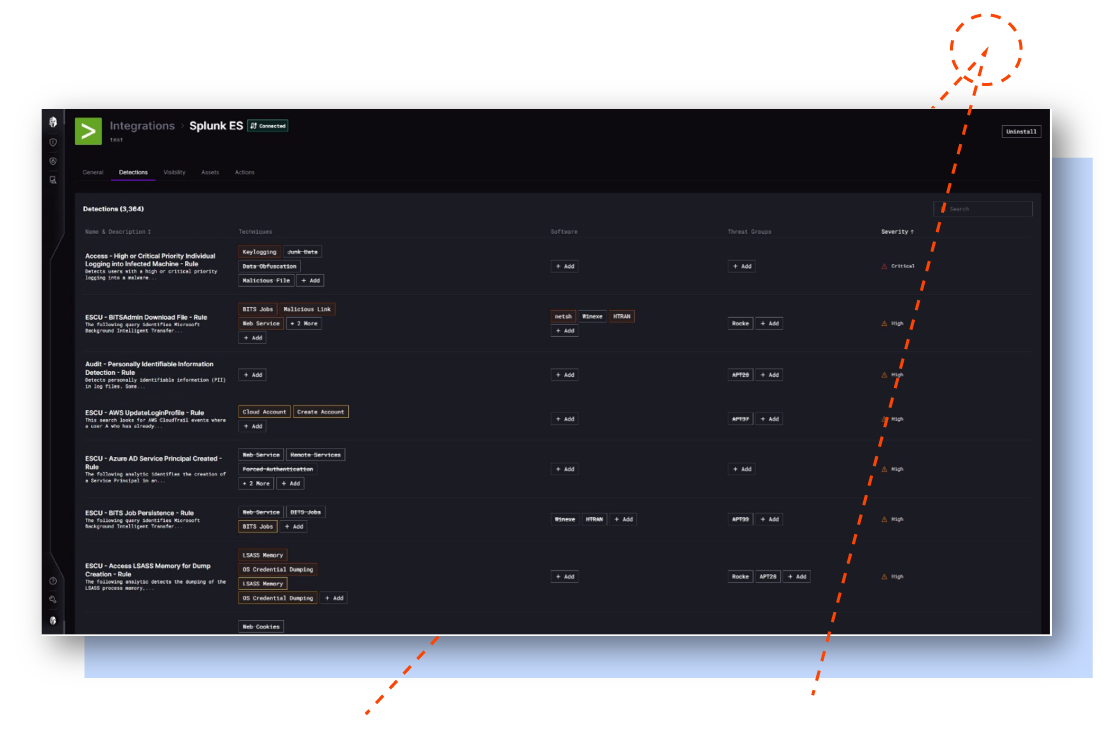
Customizable Detection Mapping
Nowadays most vendors map their detection rules to the MITRE ATT&CK framework. However, we’re still seeing some vendors distributing detection rules that aren’t mapped, incorrectly mapped, or are using old versions of ATT&CK. The Interpres platform automatically looks at each detection rule to map detections to MITRE ATT&CK and update any mappings using the old versions of ATT&CK to the newest. This has worked well, but we’ve found that some customers wish to map detection rules themselves or even modify or ignore the vendor mappings.
Conclusion
These are just a few of the features we’re primed to release. Stay tuned for our next Product & Feature Release Update with even more exciting capabilities. Customers with a current account receive updates at no additional charge.
Not a current customer?
See Interpres In Action
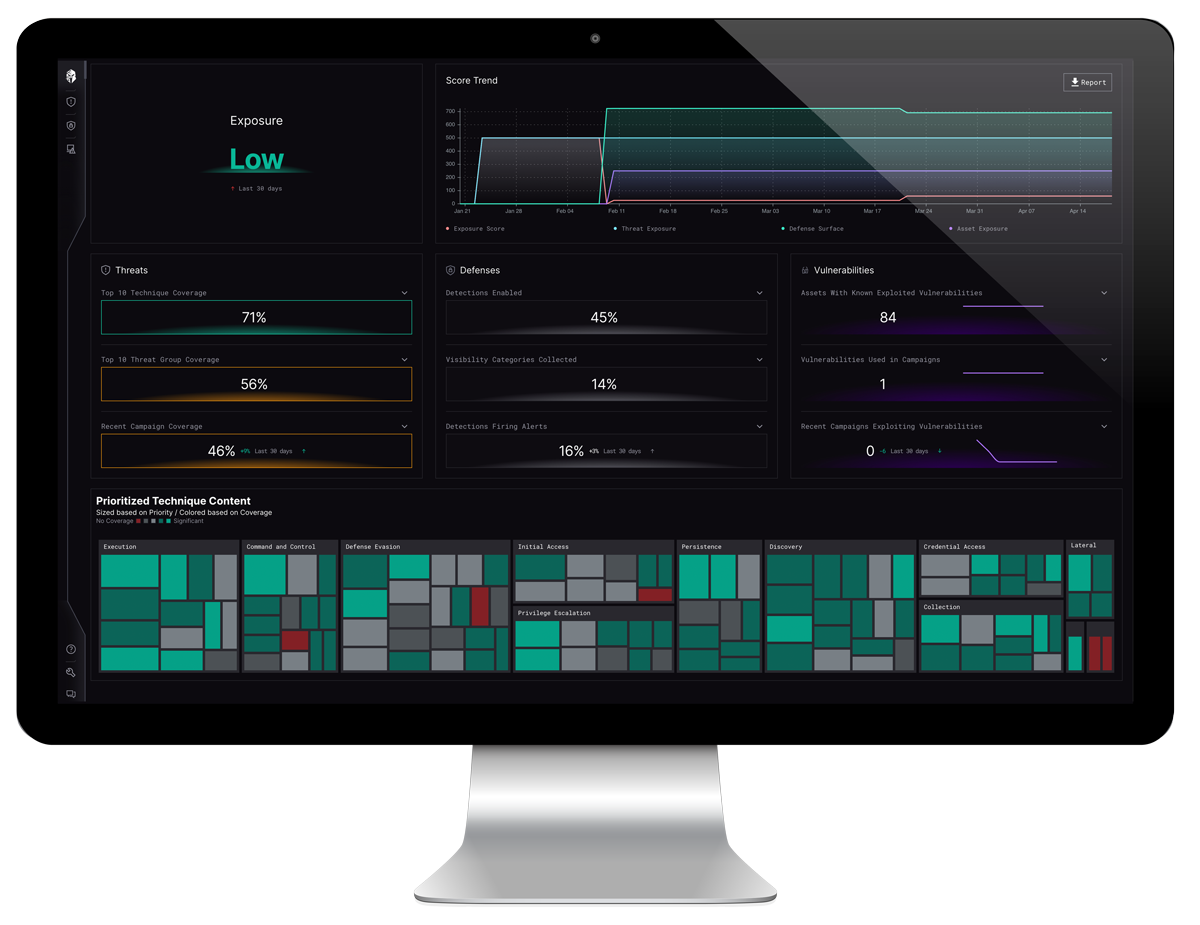
Interpres is dedicated to helping companies just like yours optimize security performance with an unbiased view of your security capabilities, so you can:
Automate your threat intelligence analysis and operationalize TTP-based threat intelligence.
Quickly identify and remediate threats and exploitable vulnerabilities likely targeting your organization.
Determine your level of cyber defense readiness against your set of prioritized threats.
Want to learn more about how we can help you start validating your cybersecurity posture?
Take a self-guided tour of the product and explore the Interpres Threat Exposure Management Platform.