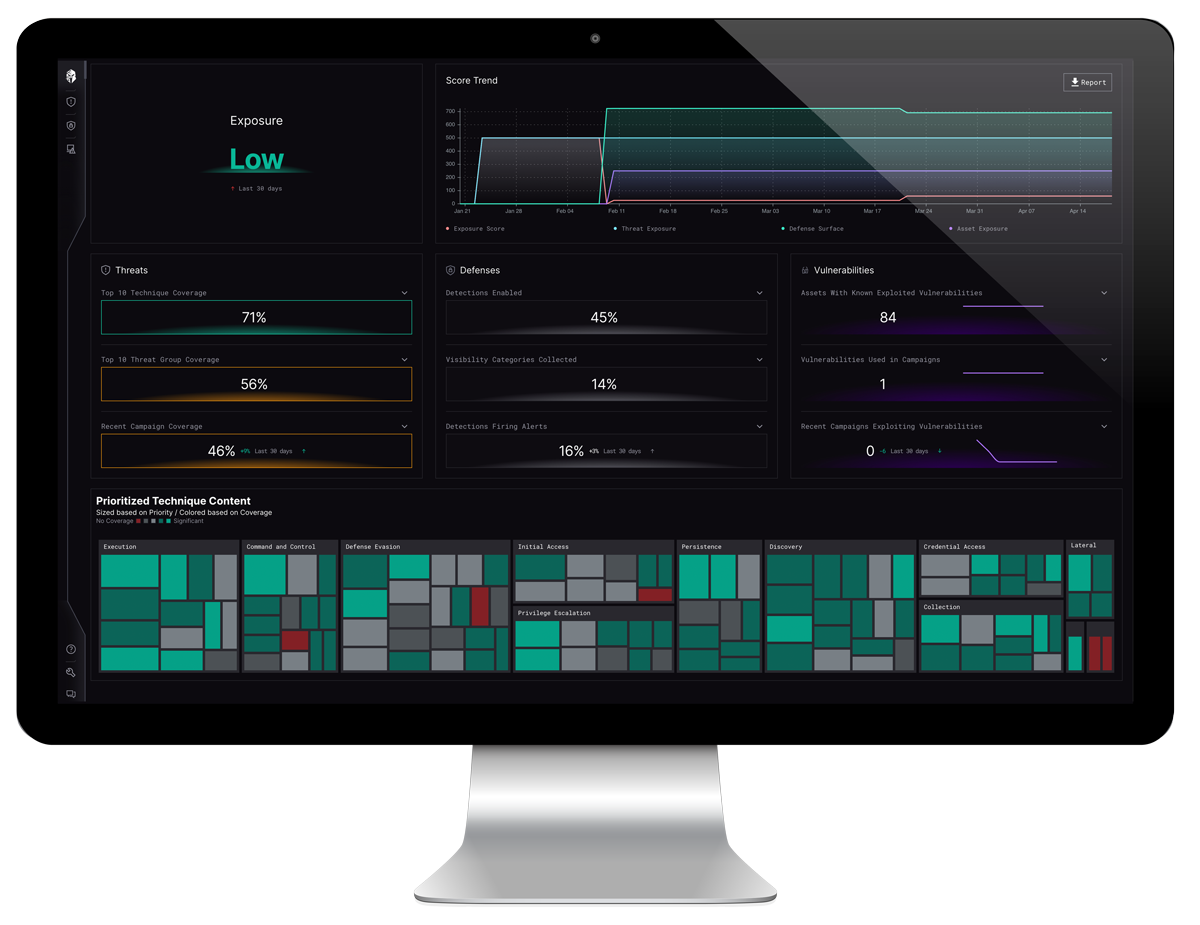
Capture a holistic view of your detection capabilities, level of detection coverage, and any coverage gaps in the context of the MITRE ATT&CK Navigator

Benefits of Automation:
- Comprehensive Coverage: Ensure detection capabilities cover a wide range of known attack techniques.
- Identification of Coverage Gaps: Systematically map existing capabilities to specific ATT&CK techniques to reveal any gaps or blind spots in defenses.
- Alignment with Threat Intelligence: Stay ahead of emerging threats and adjust detection strategies to focus on prioritized threats that pose the greatest risk.
- Efficient Resource Allocation: Streamline mapping to ATT&CK techniques, freeing up resources and maximizing the effectiveness of the security team.
- Continuous Improvement: Continuously monitor and refine detection capabilities based on changes in the threat landscape.


Key Features
THE INTERPRES ADVANTAGE

MITRE ATT&CK® Matrix

Prioritized Technique Content
Visualize detection posture in the context of prioritized MITRE Techniques delivered through the CISO Dashboard heatmap

Custom Reporting
Instantly generate detailed reports of detection capabilities, coverage, and gaps based on prioritized MITRE Techniques
Leverage Interpres for MITRE ATT&CK Analysis

Instantly understand MITRE ATT&CK coverage across your defensive ecosystem.
Minimize the risk of undetected threats and maintain an effective defensive posture against adversarial targeting.

Ensure your detection capabilities are effective against threats that pose the greatest risk to your organization.
Are you Prepared to Detect the Latest Adversary Tactics?